Avoid getting hacked 103: A guide to secure personal computers
Personal computers contain a trove of personal and sensitive information, which make them a valuable target for hackers. Here are 7 steps to improve the security of our personal computers.

This is a multi-part series about staying safe online. Lesson two explored tips on how to secure our mobile devices.
7 Tips for securing our personal computers
Our personal computers contain a trove of personal and sensitive information, which make them a valuable target for attacks. A lot of people see computer security as an overly complex and technical process. But without sweating the small stuff and focusing on the important ones, these are simple steps to improve the security of our personal computers.
Encrypt storage devices
Encrypted, encrypted and encryption. Encryption, in its simplest terms, is a method of protecting information we don’t want people to see. An example is when we are shopping online, our card details are encrypted so that "attackers" won't steal our financial information.
Setting a password on our personal devices isn’t always enough. In a scenario where an "attacker" gains physical access to our computers, the operating system password wouldn’t serve as a deterrent. Hackers can easily remove our unencrypted hard drive and connect it to another computer to have access to our files and information.
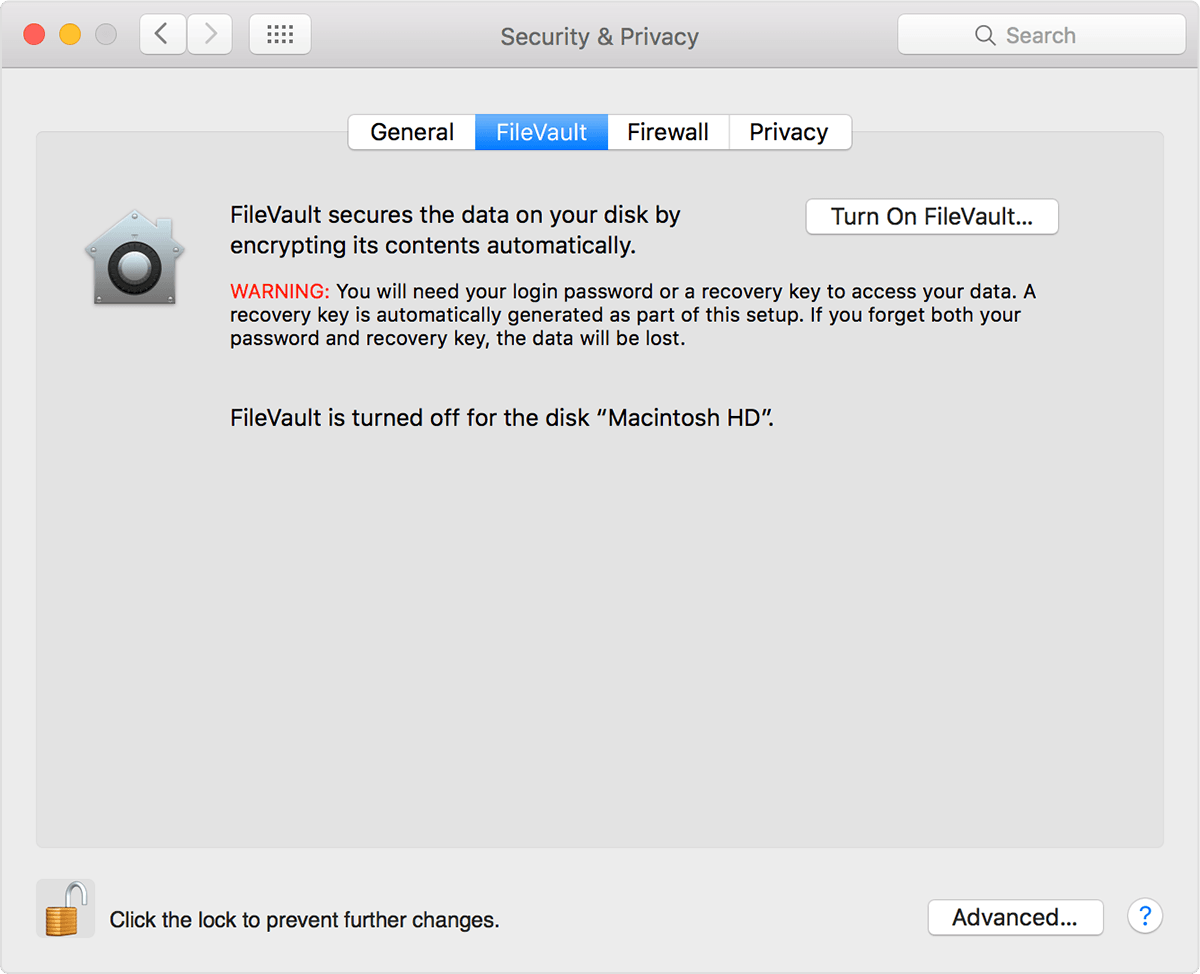
If you keep personal and sensitive information on your computer (like most people), it is necessary you encrypt your storage so that unwanted parties won’t have access to it. Most Microsoft computers have BitLocker—a trusted encryption platform—and Mac users have FileVault, which is basically Apple’s version of BitLocker.

Use secure passwords
Prior to this, we published a detailed article on the steps to creating and securing your passwords. For those that want an even more secure alternative, modern operating systems offer other passwordless means of authentication.
These include biometrics (fingerprints and facial recognition) and YubiKey (my preferred passwordless authentication option). YubiKey is a secure digital key that holds your credentials. It can be used alone or with a password as a form of MFA (multi-factor authentication).
YubiKey is a step into a passwordless future and it is already supported on the latest versions of Windows 10. Google and Facebook also support YubiKey authentication.
Update your Operating System
There are people that still use older unpatched versions of Windows and Mac operating systems. And they usually have a reason The one I hear often is: “Praise, I am not used to that windows 10.”
Updates to operating systems are not only about new fanciful user interface and additional functionalities, operating system updates contain security patches that are aimed at keeping our computers secure.
Hackers are lazy and would always take the point of least resistance –@hacksforpancakes
It is necessary that we update our operating systems and the applications that we use. This prevents attackers from taking advantage of vulnerabilities in older versions of operating systems and software to hack into our computers.
Always keep your system updated. If you have steady internet access, set up automatic updates.
Keep your Firewall enabled
A Firewall is a barricade put in place to protect our computers from malicious actors on the internet. While browsing the internet we exchange data over the network in the form of packets, a Firewall monitors these packets to ensure they are safe for our computers. It is able to do this by ensuring the packets sent and received meet a set number of rules. Any packet that doesn't meet the standard is rejected.
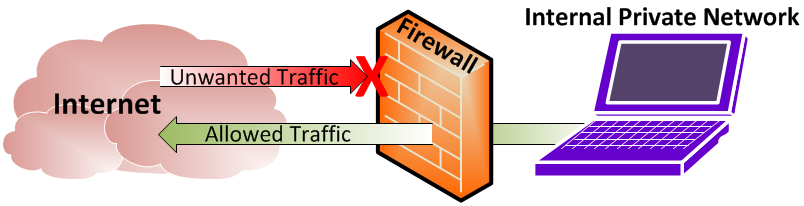
Modern operating systems have a built-in Firewall, which is good enough for most users as special configuration of a Firewall requires advanced knowledge and skills.
A Firewall can protect us while we use the internet, but it cannot block most malware, including viruses, ransomware, worms, and keylogger. This is why a Firewall must be used alongside an antivirus software.
Install Antivirus
Antivirus software protects our computer systems from malware. It is designed to protect our computers from incoming threats as well as to detect and neutralize those ones that are already on the computer.
Installing an antivirus, however, is not enough as we should ensure to update it regularly. Antivirus updates contain information about the latest malware and threats. Combining antivirus and Firewall is a good step towards securing our devices.
Backup Regularly
Storage devices can be corrupted, computer hardware can be lost, stolen or destroyed. While we may be able to get our operating system reinstalled and get a new device, the data that is lost could be gone forever. Backing up regularly helps to preserve our data in such scenarios.
There are a variety of options available for backing up the information and files on our devices, from cloud storage to physical storage devices. Physical storage devices are a cheap alternative for those that don't want to entrust cloud storage providers with their sensitive data.

Ignore Spam Mail
The best Firewalls and most expensive antivirus can’t always protect us from phishing attacks.
According to imperva.com, phishing is a type of social engineering attack often used to steal users' data, including login credentials and credit card numbers. It occurs when an attacker, masquerading as a trusted entity, tricks someone to open an email or text message and click on a malicious link. This leads to the installation of malware on the victim's device.
The best practice is to not click on unknown external email links. You can take this Google quiz to spot when you are being phished.
P.S: When buying physical storage devices for your files, it's safer to stick with known brands like Seagate, Western Digital (WD) and Toshiba Canvio. These brands offer cost-effective storage devices and you can get a 4TB External storage device for $97 (35,405 naira)







Comments ()