What are Zero-Knowledge Proofs in Crypto?
Zero-knowledge proof is a way to verify the truth of information without revealing anything else about the information itself or the prover of that information.
The growth in internet usage and online activity has allowed businesses to collect vast amounts of customer data to gain insights, and monetize user data assets. On one hand, this allows for a better and more personalized user experience. But on the other hand, since this data is usually stored in a “centralized” server, it can become vulnerable to cyber threats and data breaches.
Privacy-enhancing technologies (PETs) such as zero-knowledge proofs (ZKPs) provide ways for businesses to protect their sensitive data. In cryptography, a zero-knowledge proof or zero-knowledge protocol is a method by which one party (A) can prove to another party (B) that a given statement is true, while the A avoids conveying any additional information about themselves, apart from the facts needed to be proved.
What are zero-knowledge proofs?
A zero-knowledge proof (ZKP) is a way to verify the truth of information without revealing anything else about the information itself or the prover of that information.
It allows all manner of parties to conduct authentication with no need to exchange passwords or personal data, which means they cannot be stolen. This way, no other party can know what you’re communicating about or what files you are sharing with each other.
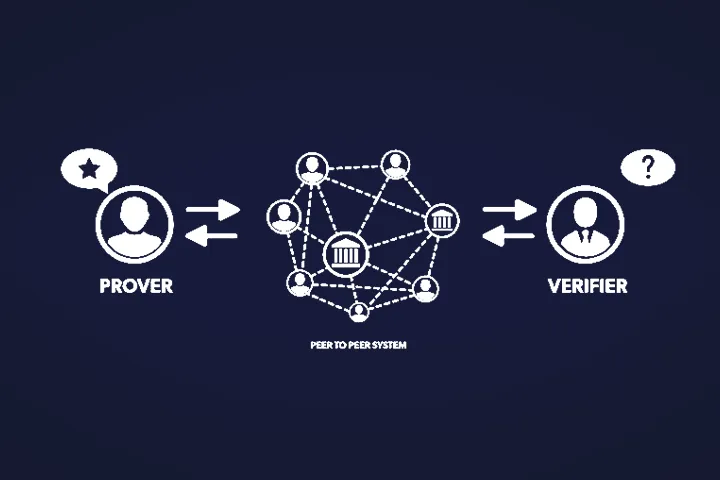
The very term “zero knowledge” originates from the fact that no (“zero”) information about the secret is revealed, but the second party (called “Verifier”) is (rightfully) convinced that the first party (called “Prover”) knows the secret in question.
How do zero-knowledge proofs work?
Let us use the popular example of a colour blind friend Charlie and his friend Dave.
Let’s say Dave (the prover) has a colour-blind friend, Charlie (the verifier) who cannot distinguish a green and a red ball from each other (have zero knowledge about whether the balls are different colours). Dave needs to prove that the colours of the balls are different but Charlie needs something more than your words to be convinced. A ZKP method for this problem would be like this:
- Charlie takes both balls and lets Dave see which ball is in which hand (green on the left, red on right).
- Then, Charlie either switches the balls between his hands or not behind his back.
- He then presents the balls to Dave and asks Dave whether he switched the balls or not. As Dave can distinguish the green ball from the red one, he can easily give the correct answer.
- Charlie is not convinced. This is because Dave has a 50% chance to correctly guess whether he switched the balls or not and the balls can still be the same colour.
- However, if Charlie repeats this several times, eventually, the probability of Dave correctly guessing whether they switched the balls or not each time would be very low. This enables Dave to verify that the balls are different colours without knowing the actual colours of the balls.
So, we can apply ZKPs in real-world applications to enable the verification of a statement. For instance, using ZKP methods, a receiver of payment can verify that the payer has a sufficient balance in their bank account without getting any other information about the payer’s balance.
Related Article: Web 3.0 promises to make computers understand data in the way humans do.
What criteria make up zero-knowledge proofs?
A zero-knowledge proof (ZKP) method must satisfy the following criteria:
- Completeness: If the information provided by the prover is true, then a ZKP method must enable the verifier to verify that the prover is telling the truth.
- Soundness: If the information provided by the prover is false, then a ZKP method must allow the verifier to refute that the prover is telling the truth.
- Zero-knowledge: The ZKP method must reveal to the verifier nothing else than whether the prover is telling the truth or not.
What are the different types of zero-knowledge proofs?
There are two main types of zero-knowledge proofs:
- Interactive zero-knowledge proofs: In this type of ZKPs, the prover and the verifier interact several times. The verifier challenges the prover who provides replies to these challenges until the verifier is convinced
- Non-interactive zero-knowledge proofs: In this type of ZKPs, proof delivered by the prover can be verified by the verifier only once at any time. This type of ZKPs requires more computational power than interactive ZKPs. They are also most preferred due to ease of user experience
Some Real World applications and use cases of zero-knowledge proofs
Zero-knowledge proofs can be used to protect data privacy in a diverse set of use cases, such as:
- Blockchain Technology: The transparency of public blockchains such as Bitcoin and Ethereum enables public verification of transactions. However, it also implies little privacy and can lead to the deanonymisation of users. Zero-knowledge proofs can introduce more privacy to public blockchains and their users.
- Finance: ZKPs can allow customers to prove that their secret number lies in a known range. For example, a mortgage applicant can prove that their income is in the admissible range without revealing their exact salary.
- Online voting: ZKPs can allow voters to vote anonymously and verify that their vote was included in the final tally.
- Authentication: ZKPs can be used to authenticate users without exchanging secret information such as passwords.
- Machine Learning: ZKPs can allow the owner of a machine learning algorithm to convince others about the results of the model without revealing any information about the ML model itself.
Particular uses of zero-knowledge proofs in blockchain
- Private transactions
Due to the principle of openness and transparency, public blockchains like Bitcoin and Ethereum allow everyone to view every transaction initiated on the public blockchain. For those with large net worths, there are concerns around privacy and data sovereignty. ZKP protocols allow parties to preserve confidentiality while conducting private and secure transactions on public blockchains
- Messaging applications
End-to-end encryption has played a big part in allowing messages to be sent privately. However, traditional messaging applications require users to verify their identity to a server. With ZKPs, an individual can prove their identity without releasing additional personal information
- Documentation
Combining ZKPs and blockchain allows users to share complex documents with security. ZKPs have the potential to encrypt data in pieces, this enables users to control certain blocks and the visibility of the information contained within them, allowing some users access while restricting others
What are the challenges of zero-knowledge proofs?
- No 100% guarantee: Even if the probability of verification by the verifier while the prover is lying can be significantly low, ZKPs don’t guarantee that the claim is valid 100%. As demonstrated above, the probability of a prover lying decreases in each iteration of the ball-picking process, but it can never reach zero. Thus, zero-knowledge proofs aren’t actual proofs in a mathematical sense.
- Computation intensity: Algorithms used are computationally intense as they require many interactions between the verifier and the prover (in interactive ZKPs), or require a lot of computational capabilities (in non-interactive ZKPs). This makes ZKPs unsuitable for slow or mobile devices
- Limited: The protocols for ZKPs usually rely on mathematical equations and numerical answers. Any other method requires a translation
- Requires large computing power: There are around 2000 computations per ZKP transaction that each require a certain amount of time to process
- Restricted: If the originator of a transaction forgets their information, all the data associated with it is lost







Comments ()