Avoid getting hacked 104: A guide to internet anonymity
Perfect internet anonymity is technically impossible, except you build everything you use. But here are some tools and steps to help improve your anonymity.

In today's technological climate, 100% anonymity on the internet is not workable.
We hear about governments spying on their citizens, and companies storing more "confidential" user data. The likes of Google and Facebook offer us "free applications" to get access to our (sign-up) data. Gmail reads every email you send and receive. Office 365 scans everything you write. Dropbox explores each file you upload. And let's not even get started on Facebook.
Achieving perfect internet anonymity is technically impossible, unless you build your internet infrastructure and write your applications.
In this article, I outline some ways in which you can improve your anonymity on the internet.
Tails
Tails is an operating system based on Linux that was built for security and anonymity. It routes all traffic through the Tor network to anonymise it. Tails comes preloaded with most of the software applications a user needs, this is to ensure that there is no need to access the internet beyond them.
Because I've used @Tails_live for years. The journalists who broke the mass surveillance revelations of 2013 all relied on it. Free, libre, and open source software projects quietly save the world every day, even when you can't see it, and their success depends on your support. https://t.co/82mQy1PlQT
— Edward Snowden (@Snowden) March 19, 2018
It also offers automatic file encryption through LUKS (Linux Unified Key Setup). If you use a USB drive, emails and chat are fully encrypted using the claws email client and pidgin for chat messaging. The pre-installed browser is a Tor-based internet client called Iceweasel. Iceweasel comes pre-configured with several security add-ons like AdBlock, HTTPS Everywhere, and NoScript.
Disposable Email as a service
There are several reasons to use disposable emails.
If you've ever signed up for an app without an intention to use it for long, a disposable email would work for you. Sometimes, all we want to do is test an app feature and not get added to a spamming mailing list of "users".
But beyond that, you might not want your email provider to spy on the content of your email. And if they do, you don't want it traced back to you.
Disposable emails provide a convenient email address that can’t be traced back to you. Some websites that provide this service for free include:
Please note that it is not advisable to use these services for illegitimate or private business. Because, you do not have control over the email domains used and cannot voluntarily flush your emails off their servers.
Encrypted Emails
Another way to improve your internet anonymity is by encrypting your emails. When you encrypt your email, your email service provider can’t scan the content of your email.
The two major protocols for email encryption are S/MIME and PGP.
S/MIME is more convenient because it is centralised and supported on most email clients, by default. Although, PGP offers a higher control over the encryption process. PGP allows users to create their encryption keys and choose the strength of the encryption that will be used. Unlike S/MIME, PGP requires third-party software to work with many popular email clients.
Virtual cards
Virtual cards are temporary debit/credit cards used to make purchases online. Their easily replaceable nature makes them suitable for one-time purchases. Thereby, protecting the user in the event of a data leak. Take, for instance, e-commerce sites.
A major proponent of ecommerce is that they make shopping more convenient. Conversely, this ease of shopping has come back to bite the industry in the back. Ecommerce sites have now become a playing ground for malicious actors (bad hackers).
These hackers create fake shopping sites or install malware into existing sites to steal user information. They steal information such as: addresses, phone numbers and credit card information. Often, the stolen user data is sold to fraudsters who then use this information to defraud the customers.
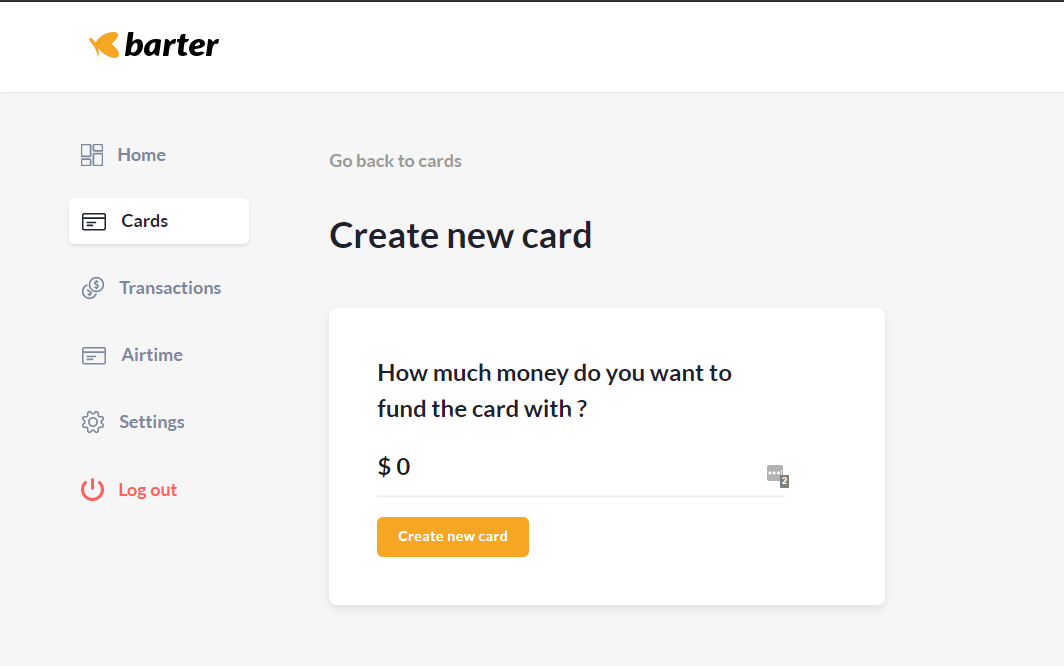
The following platforms provide virtual cards:
Tor
In most spheres, whenever people think about anonymity on the internet, Tor comes top of mind. Yet, it is last on this list because of its weaknesses.
Tor is an open-source software built to anonymise traffic. Thus, making it popular amongst privacy advocates and journalists.

Users connected to the Tor network are much harder to track. This is because Tor uses volunteer-run relays to anonymise traffic. These relays serve as nodes in the network to ensure that the data passing through it cannot be traced back to the source. However, at the exit of these nodes traffic gets decrypted so it can be sent to its intended source.
But, the downside to using Tor is that anyone can setup an exit node and spy on the unencrypted traffic sent through it.
Notable mention
Virtual Private Network: VPNs are not listed directly because many of them are not trustworthy. Three weeks ago, PCMag uncovered seven VPNs that were logging users activities, despite "no log" pledge.
Expectedly, none of the VPNs I recommended last year were on that list.
In summary, you can protect your digital footprint by making use of: Tails OS, disposable emails, email encryption protocols, virtual cards and Tor.







Comments ()